Radius protocol new vulnerability
Cybersecurity researchers have discovered a security vulnerability in the RADIUS network authentication protocol called BlastRADIUS that could be exploited by an attacker to stage Mallory-in-the-middle (MitM) attacks and bypass integrity checks under certain circumstances.
"The RADIUS protocol allows certain Access-Request messages to have no integrity or authentication checks," InkBridge Networks CEO Alan DeKok, who is the creator of the FreeRADIUS Project, said in a statement.
"As a result, an attacker can modify these packets without detection. The attacker would be able to force any user to authenticate, and to give any authorization (VLAN, etc.) to that user."
RADIUS, short for Remote Authentication Dial-In User Service, is a client/server protocol that provides centralized authentication, authorization, and accounting (AAA) management for users who connect and use a network service.
The security of RADIUS is reliant on a hash that's derived using the MD5 algorithm, which has been deemed cryptographically broken as of December 2008 owing to the risk of collision attacks.
This means that the Access-Request packets can be subjected to what's called a chosen prefix attack that makes it possible to modify the response packet such that it passes all of the integrity checks for the original response.
However, for the attack to succeed, the adversary has to be able to modify RADIUS packets in transit between the client and server. This also means that organizations that send packets over the internet are at risk of the flaw.

Other mitigation factors that prevent the attack from being potent stem from the use of TLS to transmit RADIUS traffic over the internet and increased packet security via the Message-Authenticator attribute.
BlastRADIUS is the result of a fundamental design flaw and is said to impact all standards-compliant RADIUS clients and servers, making it imperative that internet service providers (ISPs) and organizations that use the protocol update to the latest version.
"Specifically, PAP, CHAP, and MS-CHAPv2 authentication methods are the most vulnerable," DeKok said. "ISPs will have to upgrade their RADIUS servers and networking equipment."
"Anyone using MAC address authentication, or RADIUS for administrator logins to switches is vulnerable. Using TLS or IPSec prevents the attack, and 802.1X (EAP) is not vulnerable."
For enterprises, the attacker would already need to have access to the management virtual local area network (VLAN). What's more, ISPs can be susceptible if they send RADIUS traffic over intermediate networks, such as third-party outsourcers, or the wider internet.
It's worth noting that the vulnerability, which is tracked as CVE-2024-3596 and carries a CVSS score of 9.0, particularly affects networks that send RADIUS/UDP traffic over the internet given that "most RADIUS traffic is sent 'in the clear.'" There is no evidence that it's being exploited in the wild.
This attack is the result of the security of the RADIUS protocol being neglected for a very long time," DeKok said.
"While the standards have long suggested protections which would have prevented the attack, those protections were not made mandatory. In addition, many vendors did not even implement the suggested protections."
Update#
The CERT Coordination Center (CERT/CC), in a supplementary advisory, described the vulnerability as enabling a threat actor with access to the network where RADIUS Access-Request is transported to conduct forgery attacks.
"A vulnerability in the RADIUS protocol allows an attacker to forge an authentication response in cases where a Message-Authenticator attribute is not required or enforced," CERT/CC said. "This vulnerability results from a cryptographically insecure integrity check when validating authentication responses from a RADIUS server."
Web infrastructure and security company Cloudflare has published additional technical specifics of CVE-2024-3596, stating that RADIUS/UDP is vulnerable to an improved MD5 collision attack.
"The attack allows a Monster-in-the-Middle (MitM) with access to RADIUS traffic to gain unauthorized administrative access to devices using RADIUS for authentication, without needing to brute force or steal passwords or shared secrets," it
As per Secincidentdaily
RADIUS/UDP vulnerable to improved MD5 collision attacker
One such protocol is RADIUS (Remote Authentication Dial-In User Service). RADIUS was first designed in 1991 – during the era of dial-up Internet – but it remains an important authentication protocol used for remote access to routers, switches, and other networking gear by users and administrators. In addition to being used in networking environments, RADIUS is sometimes also used in industrial control systems. RADIUS traffic is still commonly transported over UDP in the clear, protected only by outdated cryptographic constructions based on MD5.
In this post, we present an improved attack against MD5 and use it to exploit all authentication modes of RADIUS/UDP apart from those that use EAP (Extensible Authentication Protocol). The attack allows a Monster-in-the-Middle (MitM) with access to RADIUS traffic to gain unauthorized administrative access to devices using RADIUS for authentication, without needing to brute force or steal passwords or shared secrets. This post discusses the attack and provides an overview of mitigations that network operators can use to improve the security of their RADIUS deployments.
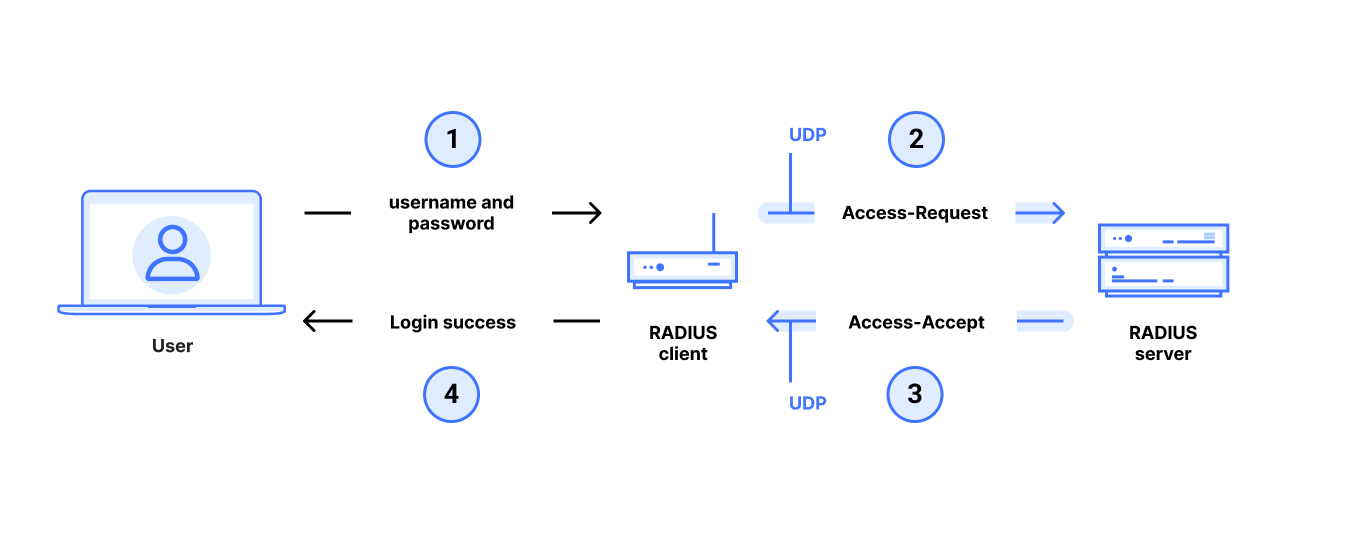
In a typical RADIUS use case, an end user gets administrative access to a router, switch, or other networked device by entering a username and password with administrator privileges at a login prompt. The target device runs a RADIUS client which queries a remote RADIUS server to determine whether the username and password are valid for login. This communication between the RADIUS client and RADIUS server is very sensitive: if an attacker can violate the integrity of this communication, it can control who can gain administrative access to the device, even if the connection between user and device is secure. An attacker that gains administrative access to a router or switch can redirect traffic, drop or add routes, and generally control the flow of network traffic. This makes RADIUS an important protocol for the security of modern networks.
Our understanding of cryptography and protocol design was fairly unrefined when RADIUS was first introduced in the 1990s. Despite this, the protocol hasn’t changed much, likely because updating RADIUS deployments can be tricky due to its use in legacy devices (e.g. routers) that are harder to upgraded
https://blog.cloudflare.com/radius-udp-vulnerable-md5-attack
Critical vulnerability in the RADIUS protocol leaves networking equipment open to attack
A new critical security vulnerability in the RADIUS protocol, dubbed BlastRADIUS (CVE-2024-3596), leaves most networking equipment open to Man-in-the-Middle (MitM) attacks. While the vulnerability can be difficult to exploit, the possible impact of an exploit is substantial.


Comments
Post a Comment